In an increasingly digital world, cloud computing has revolutionized the way organizations store, access, and manage their data. With the convenience and scalability it offers, cloud computing has become an integral part of many businesses’ operations. However, as more data privacy in cloud computing is moved to the cloud, concerns about data privacy and security have arisen. In this article, Qule will explore the importance of and discuss strategies and best practices to ensure the protection of sensitive information.
Data Privacy in Cloud Computing: Safeguarding Your Information

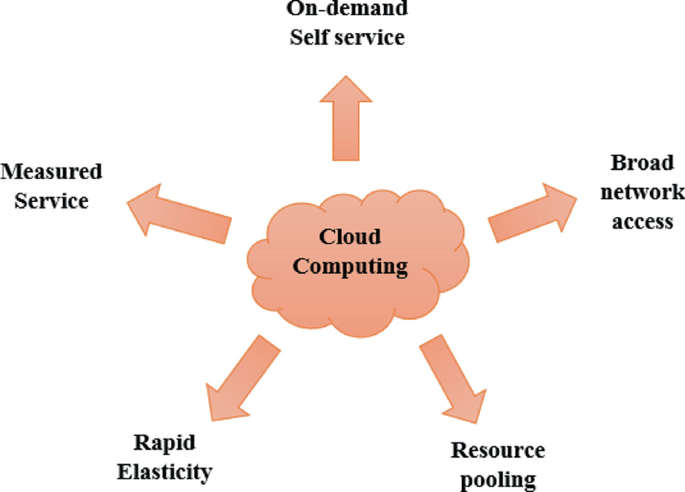
- The Rise of Cloud Computing:
Cloud computing has transformed the landscape of data storage and processing by providing on-demand access to computing resources over the internet. Organizations of all sizes have embraced cloud services for their scalability, cost-efficiency, and flexibility. Rather than relying on local infrastructure, businesses now rely on remote servers and data centers to store and manage their data. While the benefits are evident, ensuring data privacy in this new paradigm is crucial. - Understanding Data Privacy in Cloud Computing:
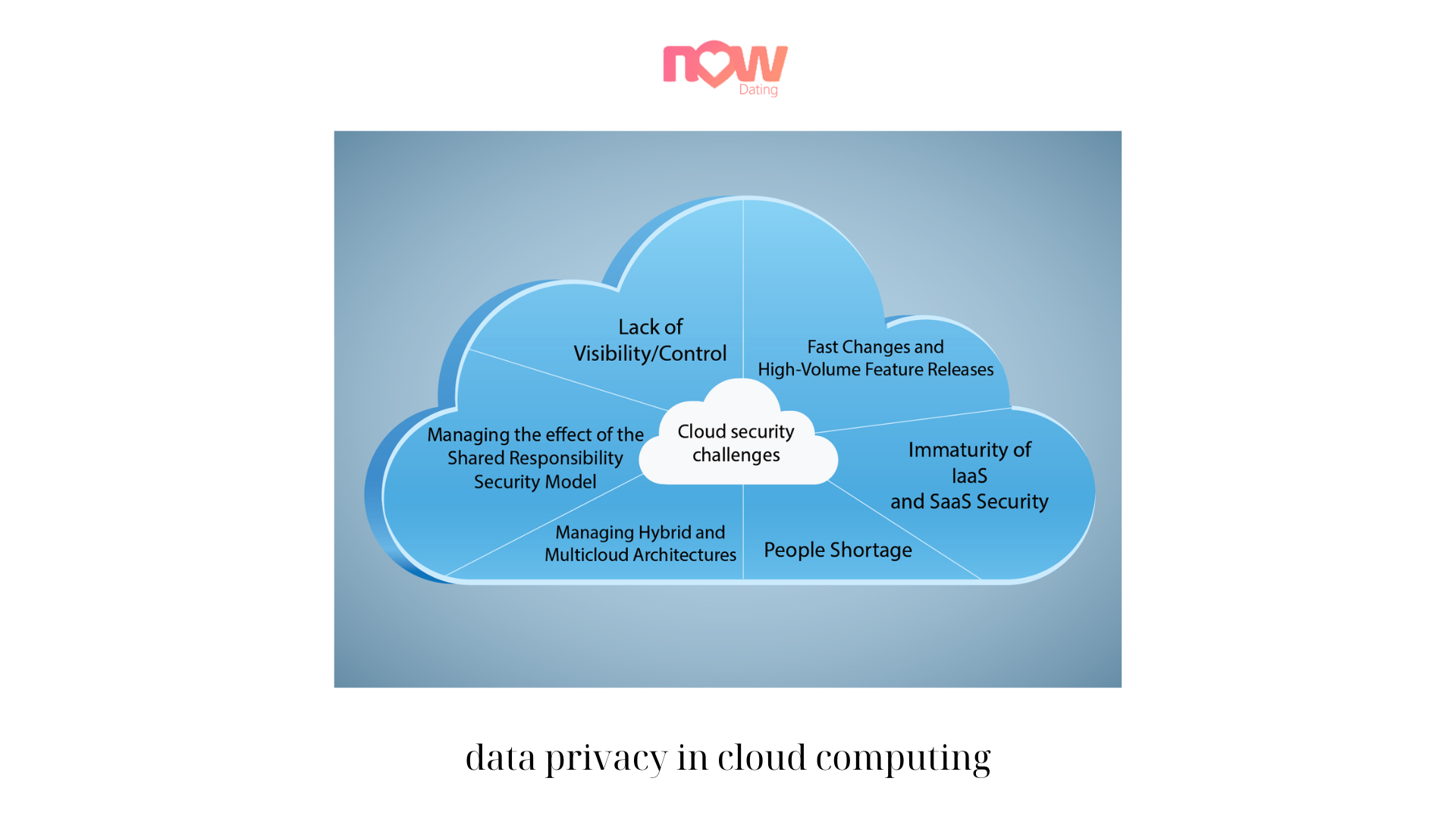
Data privacy refers to the protection of sensitive information from unauthorized access, use, or disclosure. In the context of cloud computing, it involves safeguarding data stored in the cloud against security breaches, data leaks, or unauthorized data access. This is particularly important as organizations entrust their valuable data to third-party cloud service providers. Maintaining data privacy requires a combination of technical measures, policies, and user awareness. - The Challenges of Data Privacy in the Cloud:
Cloud computing introduces unique challenges to ensuring data privacy. The shared infrastructure and multi-tenancy nature of the cloud can create potential vulnerabilities. Data may be stored alongside other users’ data, raising concerns about data separation and isolation. Additionally, data transmitted to and from the cloud can be intercepted if not adequately protected. To address these challenges, robust security measures must be implemented.
![Cloud Computing Privacy Issues [16]. | Download Scientific Diagram](https://www.researchgate.net/publication/282685380/figure/fig1/AS:391742516940801@1470410102042/Cloud-Computing-Privacy-Issues-16.png)
- Encryption as a Key Security Measure:
Encryption plays a fundamental role in protecting data privacy in cloud computing. By encrypting data before it is stored or transmitted, organizations can ensure that even if unauthorized access occurs, the data remains unreadable and unusable. Strong encryption algorithms and key management practices are essential to maintain the integrity and confidentiality of cloud-stored data. Encryption should be applied both at rest and in transit to provide end-to-end protection. - Access Controls and Authentication:
Data privacy in the cloud necessitates effective access controls and authentication mechanisms. Cloud service providers should implement granular access controls that restrict data access based on user roles and permissions. Multi-factor authentication adds an extra layer of security by requiring users to provide multiple pieces of evidence to verify their identity. Proper identity and access management practices help prevent unauthorized access and mitigate the risk of data breaches. - Data Residency and Jurisdiction:
Understanding where data is stored and the applicable jurisdiction is crucial for data privacy compliance. Different countries have varying data protection laws and regulations. Organizations must consider the legal and regulatory requirements when choosing a data privacy in cloud computing provider and ensure that data residency and jurisdiction align with their specific needs. Data sovereignty should be carefully evaluated to maintain control over sensitive information. - Data Backup and Disaster Recovery:
Data privacy in the cloud goes beyond protecting data from external threats. It also involves ensuring data availability and recovery in the event of a disaster. Data privacy in cloud computing providers should have robust backup and disaster recovery mechanisms in place to prevent data loss and enable timely data restoration. Regular backups, redundancy, and comprehensive disaster recovery plans are essential components of a robust data privacy strategy. - Transparency and Compliance:
Cloud service providers should be transparent about their data privacy and security practices. They should provide clear information about their security measures, data handling procedures, and compliance certifications. Compliance with relevant data privacy in cloud computing regulations, such as the General Data Protection Regulation (GDPR) or the Health Insurance Portability and Accountability Act (HIPAA), is crucial for maintaining data privacy. Organizations should carefully evaluate a provider’s compliance posture before entrusting them with their data. - User Education and Awareness:
Data privacy is a shared responsibility between cloud service providers and users. Organizations must educate their employees about best practices for data privacy in the cloud. This includes raising awareness about potential risks, training users on secure data handling practices, and promoting a culture of data privacy. Regular security awareness programs and training sessions can significantly contribute to mitigating the human factor in data breaches. - Regular Audits and Assessments:
To ensure ongoing data privacy and security, regular audits and assessments should be conducted. Organizations should periodically review their cloud service provider’s security controls and practices, assess the effectiveness of their data privacy measures, and identify areas for improvement. External audits or independent security assessments can provide an objective evaluation of the provider’s security posture and help maintain a high level of data privacy.
Conclusion:
Data privacy in cloud computing is a critical concern for businesses in today’s digital landscape. As organizations increasingly rely on cloud services to store and manage their data, protecting sensitive information becomes paramount. By implementing robust security measures, such as encryption, access controls, and authentication mechanisms, combined with user education and compliance with data protection regulations, organizations can safeguard their dataand maintain privacy in the cloud. Regular audits and assessments ensure that data privacy practices remain effective and up to date. By prioritizing data privacy in cloud computing, organizations can leverage the benefits of the cloud while maintaining the trust and confidence of their customers and stakeholders.
Conclusion: So above is the Data Privacy in Cloud Computing: Safeguarding Your Information article. Hopefully with this article you can help you in life, always follow and read our good articles on the website: qule.info
Related Articles
-
How The First Cloud Service Provider WorksFebruary 15, 2023